Identification: CVE 2017-11882
CVSS Base Score: 7.5
CVSS Vector: AV:N/AC:L/Au:N/C:P/I:P/A:P
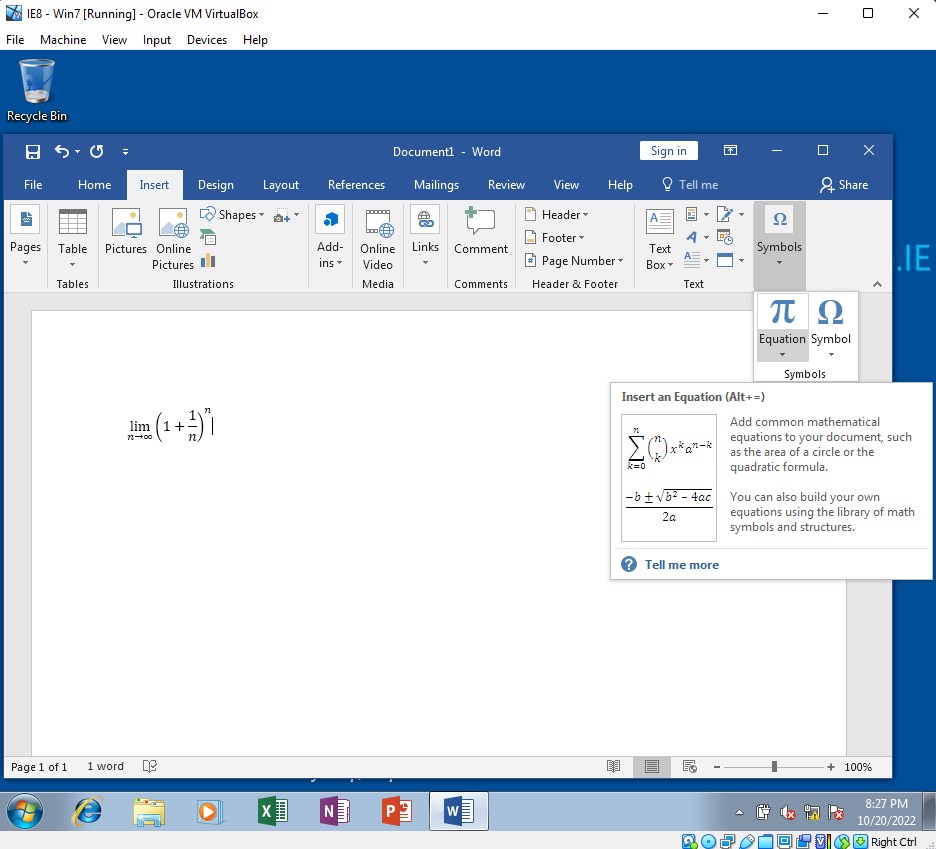
A tool used to format and display equations within Microsoft Office 2016, and some of the Microsoft Service Packs from 2007, 2010, and 2013, contains a pretty nasty vulnerability called Microsoft Office Memory Corruption. The way it works is that the process that handles this Equation Editor, called eqnedt32.exe, doesn't follow Data execution prevention (DEP) and address space layout randomization (ASLR) unless users were universally using those: Word wasn't running the process, so Microsoft Office's security settings would have no effect.
Why is that a problem? Well, if an attacker can get you to just open a document that secretly contains not just an equation but some malicious code, they can force your computer to execute commands they embedded when that document was created.
According to CISA, attackers continue to exploit this vulnerability because Microsoft Office is used so ubiquitously. There is a patch that anyone using those versions of software should use... if they've been good about keeping updates & patches. Unfortunately, if someone's got an out-of-date Office suite running on Windows 7 and and haven't disabled Equation Editor, this can still be used against them.
Most of us don't need to worry about this anymore. Windows operating systems starting at Windows 8.0 have address space layout randomization for the entire system... IF it's configured to use the ASLR. Between Windows 8.0 and Windows 10, this fix has to be specifically protected to guarantee its use in all cases (something about non-DYNAMICBASE code). If you're stuck using Windows 7, then as usual, the best defense against this specific vulnerability is keeping software up-to-date including all security patches. When this first emerged, and against any unprotected system, the possibilities for exploitation were limitless.
Here's what the Equation Editor feature in Microsoft Office 2016 looks like on a Windows 7 virtual machine:
Thanks to @cybercdh for a wonderful explanation of this vulnerability, which can be found here.
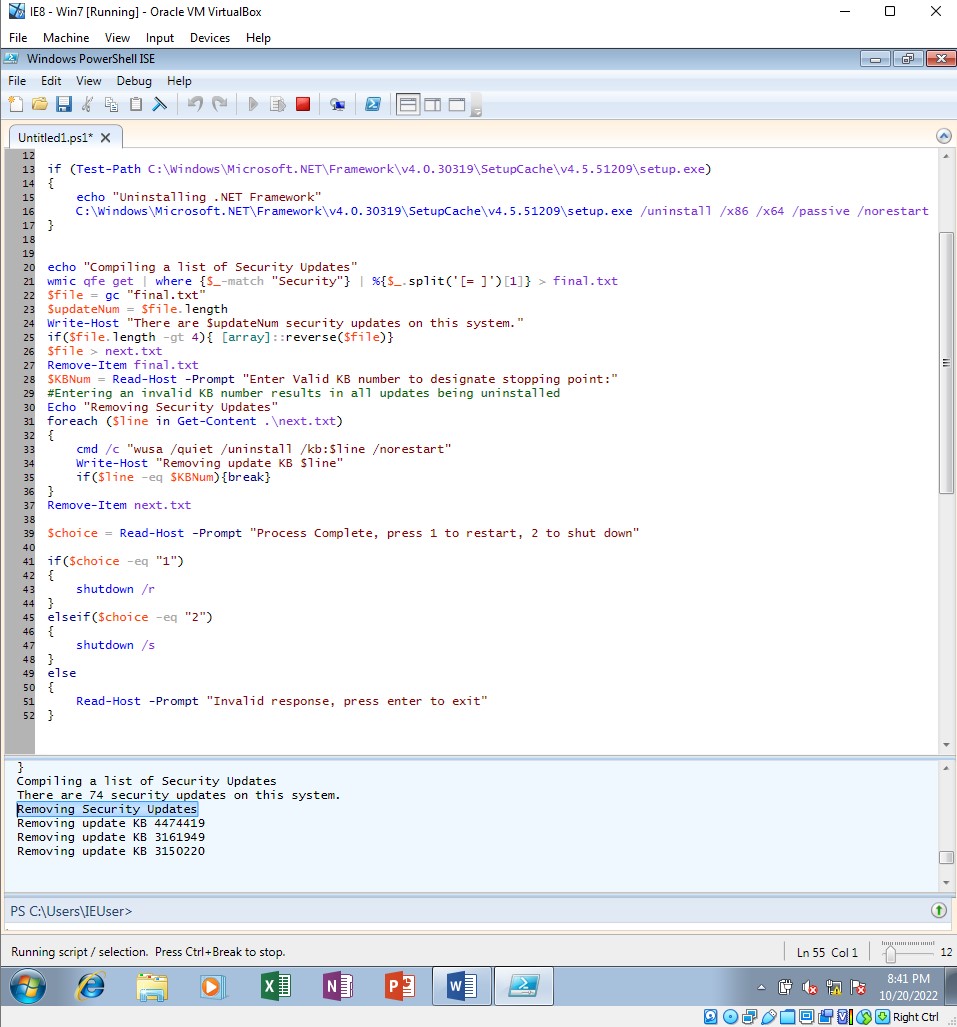
By the way, have you ever wanted to make your system vulnerable? Here's a script that will remove security patches.
Note: this is only a good idea for learning on an isolated VM. Apply with care.